UPDATE AS OF 1/15/21: Hack’s Total Costs for Cyber Insurers Has Exceeded $90m
UPDATE AS OF 12/21/20: Microsoft’s Powerful Response
Microsoft has taken four dramatic steps to counterattack A.P.T. 29’s initial strike.
1) On December 13th, the day Cozy Bear’s attack became public, Microsoft announced that it removed the digital certificates used by the Trojaned files. These certificates tricked Windows systems into believing that the compromised files were legitimate. This step essentially told Windows systems to stop trusting those files, which in turn could stop them from being used.
2) Next, Microsoft announced updates to its Windows Defender anti-malware. The updates empowered Defender to detect and alert users if the Trojaned files were found on the system.
3) Next, on Tuesday, Dec. 15th, Microsoft and others moved to “sinkhole” one of the domains that the malware was using for command and control (C2): avsvmcloud[.]com. Sinkholing is a legal tactic in which an organization like Microsoft petitions in court to seize control of a domain being used for malicious purposes away from its current owner, in this case, A.P.T. 29.
When successful, the organization can then use its ownership of that domain to interrupt the attacker’s control over the malware and the systems it has infected. Sinkholed domains can also be used to help identify compromised systems: when the malware reaches out to the sinkholed domain for instructions, the new owners can identify those systems and attempt to locate and warn the owners. Sinkholing is a tactic that was first used in big attacks in the 2008-2009 battle against Conficker and has been a standard tactic in Microsoft’s toolkit for years, including most recently against TrickBot.
4) Finally, on Wednesday, Dec. 16th, Microsoft changed its phasers from “stun” to “kill mode” by changing Defender’s default action for the infected files from “Alert” to “Quarantine.” This action could cause systems to crash but will kill the malware when it’s found.
Thanks to these steps, the attackers were left with control of barely a tiny fraction of infected systems. That said, they may still have access to compromised networks through other means; those investigations remain ongoing For example, Cozy Bear may no longer control the machines on a network, but may still have access email systems.
Related: BCP Tech Broker SolarWinds Update
Hackers Had Free Access to Federal Email Networks
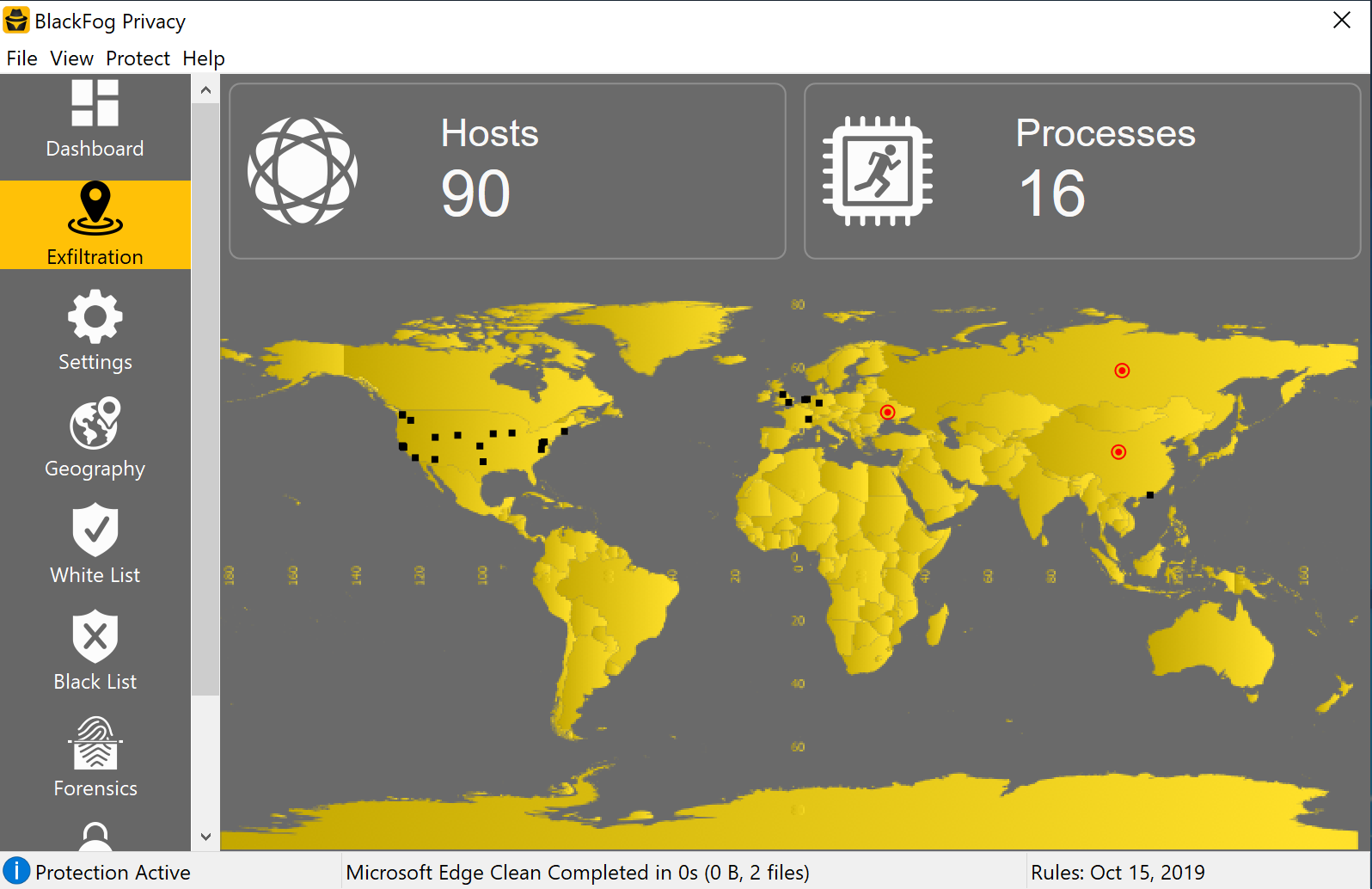
Supply chain attack was executed via SolarWinds.
The Trump administration has publicly acknowledged that state-sponsored foreign hackers — almost certainly tied to a Russian intelligence agency called A.P.T. 29 (aka Cozy Bear) — stealthily broke into a multiple government email networks, including those of the Treasury and Commerce Departments.
Forensic reports show that these hacks began sometime in early 2020, meaning they went unnoticed all throughout the Presidential Election. “The United States government is aware of these reports, and we are taking all necessary steps to identify and remedy any possible issues related to this situation,” John Ullyot, a spokesman for the National Security Council, said in a statement.
It appears that a main target was the National Telecommunications and Information Administration, which determines policy for cyber threats, and also sets standards for blocking imports and exports of technology that is considers a risk to national security. For example, China has been repeatedly found to pre-install malware on devices before they are shipped to other countries.
Late Sunday night, all government agencies were forced to shut down all use of network management software made by a company called SolarWinds. The order was so urgent that “completion reports” were required by Monday from all agencies confirming that the software was no longer in use. The malicious code was injected when the hackers broke into automatic updates of the software (just like when your iPhone automatically updates overnight).
Cybersecurity firm FireEye was the first to notice the hack after its own systems were penetrated, and reported their assumption that both government and other private entities had been hacked as well. “There appear to be many victims of this campaign, in government as well as the private sector,” said Dmitri Alperovitch, who was the co-founder of CrowdStrike, the cybersecurity firm that helped find the Russians in DNC systems during the 2016 Presidential Election.
Related: Read the NSA’s Official Warning
What was the goal of the attack?
Investigations into Russia’s motives remain ongoing, but almost all state-sponsored cyber events revolve around a these goals:
A) To gather intelligence.
FireEye, the cybersecurity firm mentioned above, do quite a bit of work for Department of Homeland Security and other federal intelligence agencies. They hire the firm to conduct expert-level, benign hacks of their systems, a strategy called penetration testing. By hacking FireEye, Russia can access the results of these tests, and the means FireEye uses to conduct them. FireEye is far from the only private victim in this attack, but perhaps the most notable.
Because the hackers had access to US Treasury and Commerce Department email systems, they could also have gathered information the old-fashioned hacker way… by combing through inbound and outbound messages from agency accounts.
B) To send future emails posing as US Government employees.
By gaining information about the email habits of federal employees, the hackers are can leverage these patterns for future attacks. Phishing attacks in general have increased 668% since the beginning of the recent pandemic, and governments and private companies alike should take serious measures to protect employees who work from home offices.
C) To impact or otherwise muddy the 2020 Presidential Election, and incite fear/panic in the United States.
Look no further than this article about the Russian involvement in the 2016 Democratic National Convention.
The history of Russian theft of critical data from the U.S. government stretches more than two decades and resulted in the creation of United States Cyber Command, the Pentagon’s quickly expanding cyberwarfare force. As early as the mid-1990s, the F.B.I. was called in for an investigation into networks that included Los Alamos and Sandia National Laboratories, which work on nuclear weapons design, among other issues.
How do these threats impact SMEs in the United States?
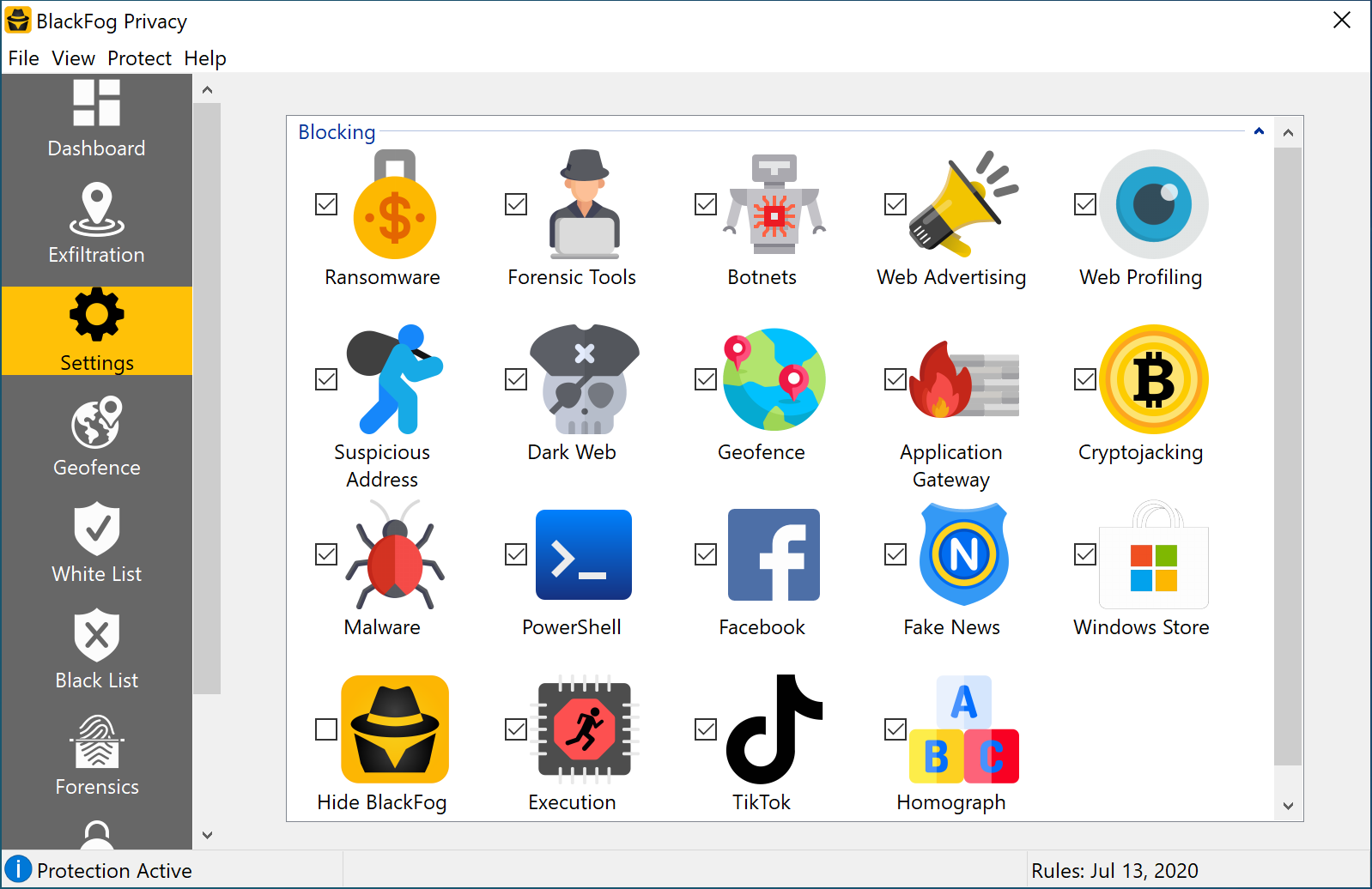
The potential impact “supply chain attacks” can have on American businesses is similar to the impact this attack has had on US Federal agencies. If a hacker manages to infect a 3rd party software application used by your business, it could enable them to directly download malware/ransomware onto your network, or launch phishing/spear phishing attacks from your employees company email accounts. Ouch.
Are supply chain hacks covered by Evolve’s cyber insurance?
Yes. Here’s how Evolve covers ransomware and phishing-related funds transfer fraud.
Evolve’s cyber policy agrees to reimburse the Insured for any ransom paid by the Insured, or on the Insured’s behalf, in response to an extortion demand first discovered by you during the period of the policy as a direct result of any threat to:
-
-
-
- introduce malware, or the actual introduction of malware, including Ransomware, into your computer
systems;
- prevent access to your computer systems or data or any third party systems hosting your applications
or data;
- reveal your confidential information or confidential information entrusted to you; or
- damage your brand or reputation by posting false or misleading comments about you on social media
sites.
In addition the the ransom payment itself, ransomware attacks often require data restoration and/or data recreation. Evolve intends to cover those costs, as well as IT Security and Forensic Costs ($500/hr), Crisis Communication Costs ($500/hr), and in the case of a privacy breach accompanying the ransomware attack, we cover both 1st and 3rd Party Privacy Breach Management Costs ($1-3 per individual).
- Funds Transfer Fraud via Phishing attack
Evolve’s cyber insurance policy covers both 1st party and 3rd party bank accounts. If the Insured suffers a BEC attack and the hackers successfully trick one of the Insured’s vendors to wire money to a fraudulent bank account, Evolve would cover the losses of the vendor in aggregate up to the policy limit.
If the vendor were the one whose email account is hacked, and the criminals convince an Evolve Insured to wire money to a fraudulent account, then the Insured would be covered on an each and every claim basis up to the policy limit.